This website stores cookies on your computer. These cookies are used to collect information about how you interact with our website and allow us to remember you. We use this information in order to improve and customize your browsing experience and for analytics and metrics about our visitors both on this website and other media. To find out more about the cookies we use,
see our Privacy Policy.
SonicWall Showcase
Introducing the New SonicWall TZ Series
The SonicWall TZ series of firewalls is designed to deliver enterprise-class security without the enterprise-grade complexity and price. With zero-touch deployment and simplified centralized management, installation and operation is easy. Detect sophisticated threats, including encrypted attacks, with advanced networking and security features, like the multi-engine Capture Advanced Threat Protection (ATP) and cloud-based sandbox service with patent-pending Real-Time Deep Memory Inspection (RTDMI™). Optional PoE/PoE+ support and Wi-Fi features allow you to create a unified security solution for both wired and wireless networks.
- Manage everything from one location with single-pane-of-glass management and reporting
- Integrate SonicWall Secure SD-WAN without an additional license
- Advanced threat protection that doesn’t compromise network performance
- Zero-touch deployment capability, built-in and expandable storage, and redundant power


Cybercriminals Have Never Been Stealthier
Stop them with SonicWall’s next-gen firewalls’ malware analysis, encrypted traffic inspection, and cloud app securitySonicWall Cloud App Security
As an integral component of the SonicWall Capture Cloud Platform, the SonicWall Cloud App Security (CAS) extends the most complete defense in-depth security stack for Office 365 and G Suite users. CAS helps stop targeted phishing and zero-day attacks that bypass Microsoft, Google, and Secure Email Gateway security filters. Its API-based, multi-layered inline threat prevention system is invisible to hackers and enables full suite protection for cloud email and SaaS applications. The solution easily deploys within minutes and employs a combination of machine learning, artificial intelligence, and big-data analyses to provide powerful anti-phishing, attachment sandboxing, click-time URL analysis, impersonation, and data leakage protection.SonicWall Capture Client
The ever-growing threat of ransomware and other malicious malware-based attacks has proven that client protection solutions cannot be measured on endpoint compliance alone. Traditional antivirus technology uses a long-embattled signature-based approach, which has failed to match the pace of emerging malware and evasion techniques. Additionally, the proliferation of telecommuting, mobility, and BYOD, had caused a dire need for consistent protection for endpoints anywhere.SonicWall Network Security Manager
As the number of firewalls in your organization grows, so too does the challenge of managing them. SonicWall Network Security Manager (NSM) scales with your organization and your security needs. From a single console, you can orchestrate all firewall operations, see hidden risks, discover misconfigured policies, and make compliance easier with a full audit trail. With SonicWall NSM, centralize firewall management and gain more capability, not more complexity.SonicWall Secure SD-WAN
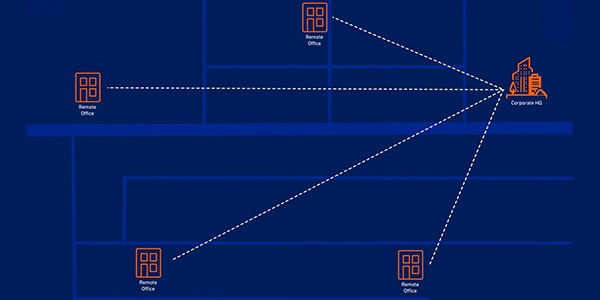
SD-WAN technology allows organizations with branch locations to build highly available and higher-performance WANs. By using low-cost Internet access, including broadband, 3G/4G/LTE, and fiber, organizations can cost-effectively replace expensive WAN connection technologies, such as MPLS with SD-WAN. SonicWall delivers comprehensive, industry-leading security solutions that simplify SD-WAN deployments.Zero Trust Access
Remote work, the growth of BYOD, employee mobility, and the use of cloud-based applications are all on the rise, and perimeter-based security isn’t enough to protect your organization in this new, hyper-distributed era. Zero Trust Access (ZTA) is the next-generation security approach that is made for the cloud era and will become the standard of tomorrow’s secure access.Let’s Connect!
Our security experts can help ensure your organization is protected from today’s threats as well as tomorrow’s. Fill out the form below, and we’ll be in touch shortly to help you start creating a security plan that meets your needs.Read Transcript
Batch Add Products by Item #
15